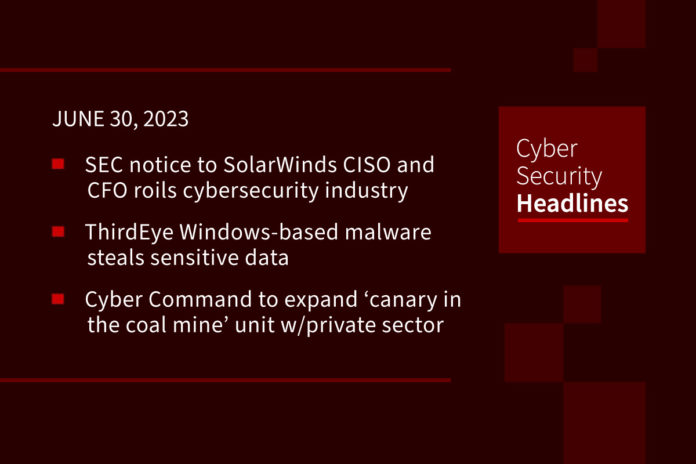
SEC notice to SolarWinds CISO and CFO shakes up cybersecurity industry
US SEC staff have recommended legal action against individual SolarWinds employees, in an unusual move that is causing a stir among cybersecurity professionals. Current and former employees and officers of the company including the CFO and CISO have received so-called Wells notices from the SEC staff, in connection with the investigation of the 2020 cyberattack, the company said in an SEC filing. The notices allege that the company violated federal securities law by not having internal cybersecurity controls in place to prevent the attack. A SolarWinds spokesperson defended the company’s response to the fiasco but said its executives may face charges related to their handling of the situation.
(The Record and CSO Online)
Newly uncovered ThirdEye Windows-based malware steals sensitive data
ThirdEye is a previously undocumented Windows-based information stealer which is capable of harvesting sensitive data from infected hosts. It has already been seen in the wild. Fortinet’s FortiGuard Labs stated that it discovered the malware within an executable disguised as a PDF file with a Russian name that translates to “CMK Rules for issuing sick leaves.pdf.exe.” The stealer can gather information system metadata and register usernames and volume information, and then transmit the data to a C2 server, using the string “3rd_eye”.
Cyber Command to expand ‘canary in the coal mine’ unit working with private sector
A little-known program that operates as one of the military’s chief links to private industry is getting an upgrade. Its staff, comprised of military and civilian technical experts will grow from twelve to twenty-four people by this time next year, according to Army Lt. Col. Jason Seales, the command’s chief of private sector partnerships. During a recent interview at the NSA’s Cybersecurity Collaboration Center (CCC), he said, “We need to make sure that we have additional resources and capabilities available … and not put the burden so much on the small handful of folks that we have now.”
Microsoft Sysmon now detects when executables files are created
Sysmon 15 is a new version of a free product from Microsoft that monitors and blocks malicious or suspicious activity and then log the events to the Windows Event Log. This newest version converts the detection into a protected process and adds a ‘FileExecutableDetected’ option to log when executable files are created. In its role as a detector of malicious behavior, Sysmon is often targeted by threat actors who naturally want to disable it. By converting the Sysmon.exe executable into a protected process, Microsoft expects greater prevention of malicious code being injected.
Thanks to this week’s episode sponsor, AppOmni

Lawsuit says OpenAI violated US authors’ copyrights to train AI chatbot
OpenAI faced a legal challenge in San Francisco federal court last Wednesday, with two U.S. authors presenting a proposed class action that states the company “misused their works and that of other authors to ‘train’ ChatGPT, by mining data copied from thousands of books without permission, infringing the authors’ copyrights.” This is not the first lawsuit of its kind. Several additional legal challenges have been filed over material used to train AI systems, including source-code owners against OpenAI and Microsoft’s GitHub, and visual artists against Stability AI, Midjourney, and DeviantArt.
(Reuters)
Android spy app LetMeSpy suffers data breach
Makers of the Android-based phone monitoring app LetMeSpy have revealed that a security breach that occurred on June 21, affecting sensitive data belonging to thousands of Android users. LetMeSpy is a subscription based app that allows its customers to “snoop on others by installing the software on their devices.” It is marketed as a tool for parental or employee control. It can collect call logs, SMS messages, and geolocations, and its icon can be hidden from the device’s home screen launcher. The stolen data is email addresses, messages, and victims’ locations going back to 2013.
Flutter-based Android malware targets credit cards and 2FA codes
The Android malware family called Fluhorse is being revealed by security specialists as “a significant shift…that… incorporates the malicious components directly within the Flutter code.” This according to Fortinet FortiGuard Labs researcher Axelle Apvrille, in a report published last week. Fluhorse was first identified by Check Point in early May of this year. It uses phishing as its point of entry, with the mission of stealing credentials, credit card details, and two-factor authentication (2FA) codes.
Sony’s confidential PlayStation secrets spilled because of a Sharpie
Confidential information about Sony’s PlayStation operations has been revealed by mistake. As reported in The Verge, “as part of the FTC v. Microsoft hearing, Sony supplied a document from PlayStation chief Jim Ryan that includes redacted details on the margins Sony shares with publishers, its Call of Duty revenues, and even the cost of developing some of its games.” However the redactions were made with a common black Sharpie marker which allowed the text to remain visible when placed on a scanner. Sony’s competition quickly downloaded the documents before they were taken down. The redacted material allegedly reveals details such as the cost of development of some of its games, the costs and dangers of Microsoft making Call of Duty exclusive to Xbox, and the true value of Call of Duty to PlayStation.